Beyond Firewalls: Strengthening Your Business’s Cyber Defenses
As cybersecurity threats rapidly evolve, firewalls alone cannot ensure your…
If you have been around IT long enough, you remember the early excitement around cloud migration. The pitch was simple: pick up your servers, drop them in the cloud, and...
If you run a business in India that collects, stores, or processes personal data — and let’s be honest, almost every modern business does — there is a law you...
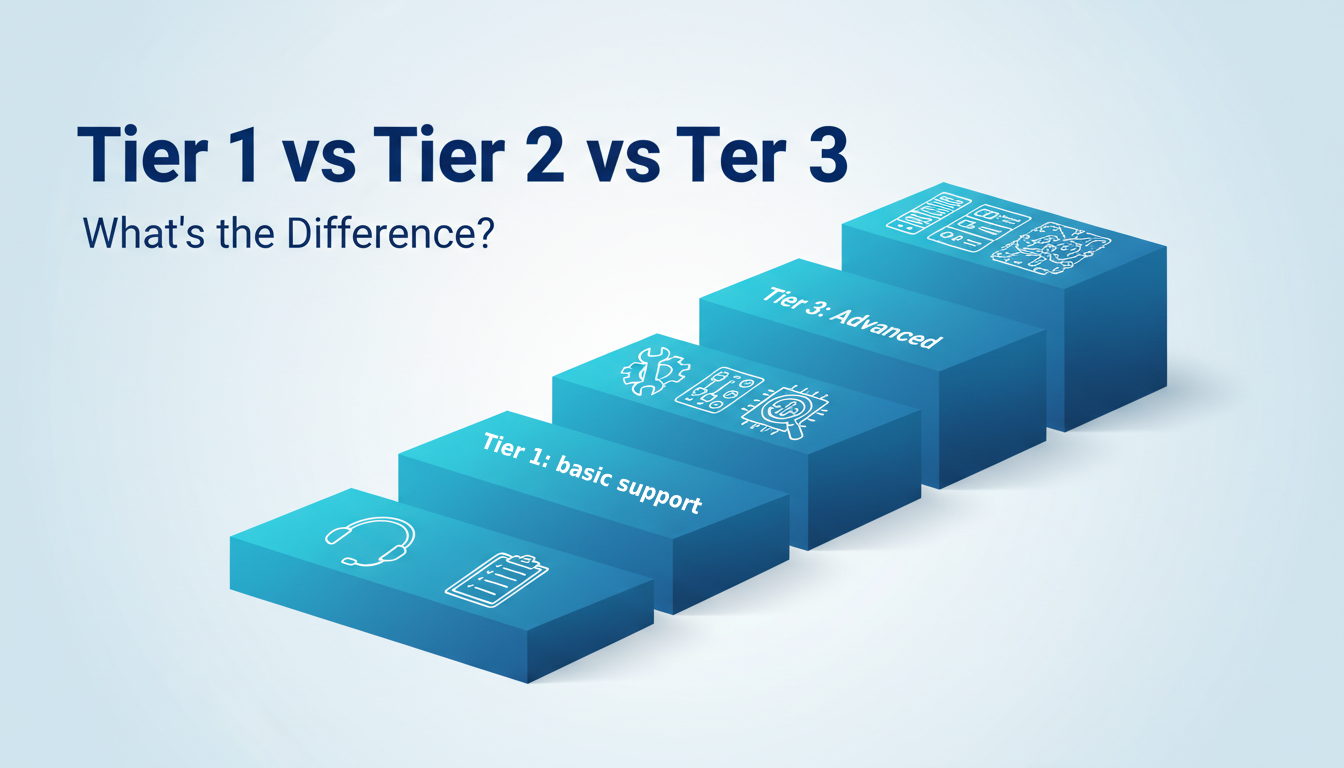
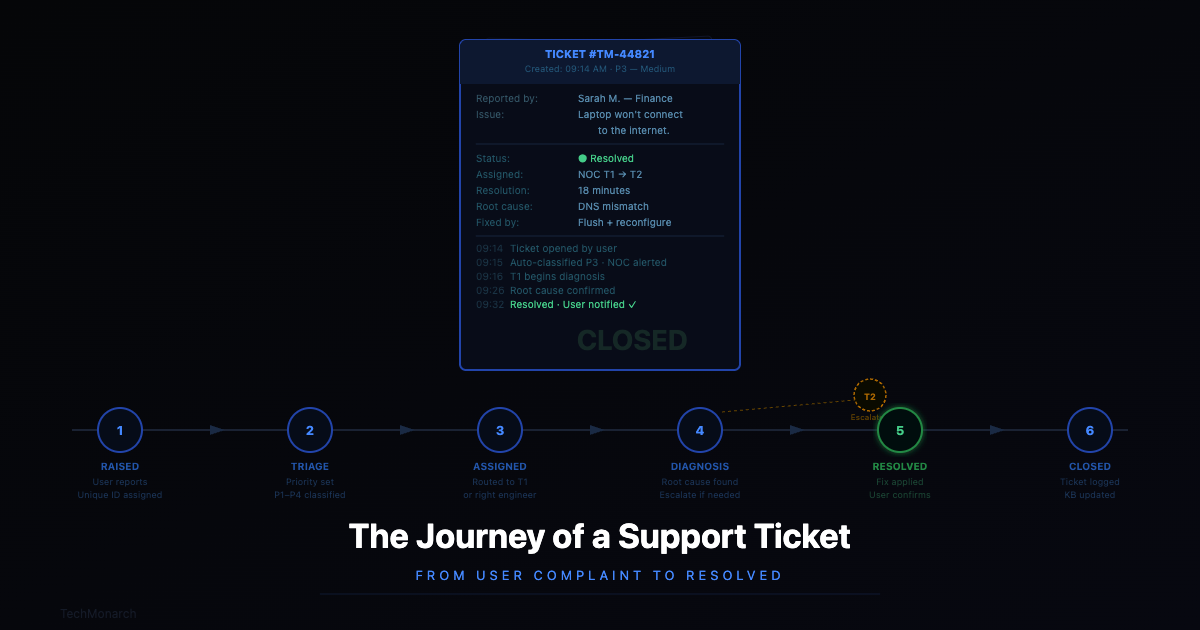
If you have ever called IT support, you have probably noticed that your first call does not always land you with the person who actually fixes the problem. Someone logs...
Make in Their First Three Years Starting a company is exhilarating. You have got the idea, the team, maybe even the first few clients. Everyone is moving fast, wearing multiple...
Imagine coming into work one morning and finding that every computer in your office is locked. Every file — encrypted. A message on screen demands a ransom in cryptocurrency. Your...
Let’s be honest — there’s a specific kind of frustration that comes with a slow computer. You click something, nothing happens. You wait. You click again. The spinning wheel of...
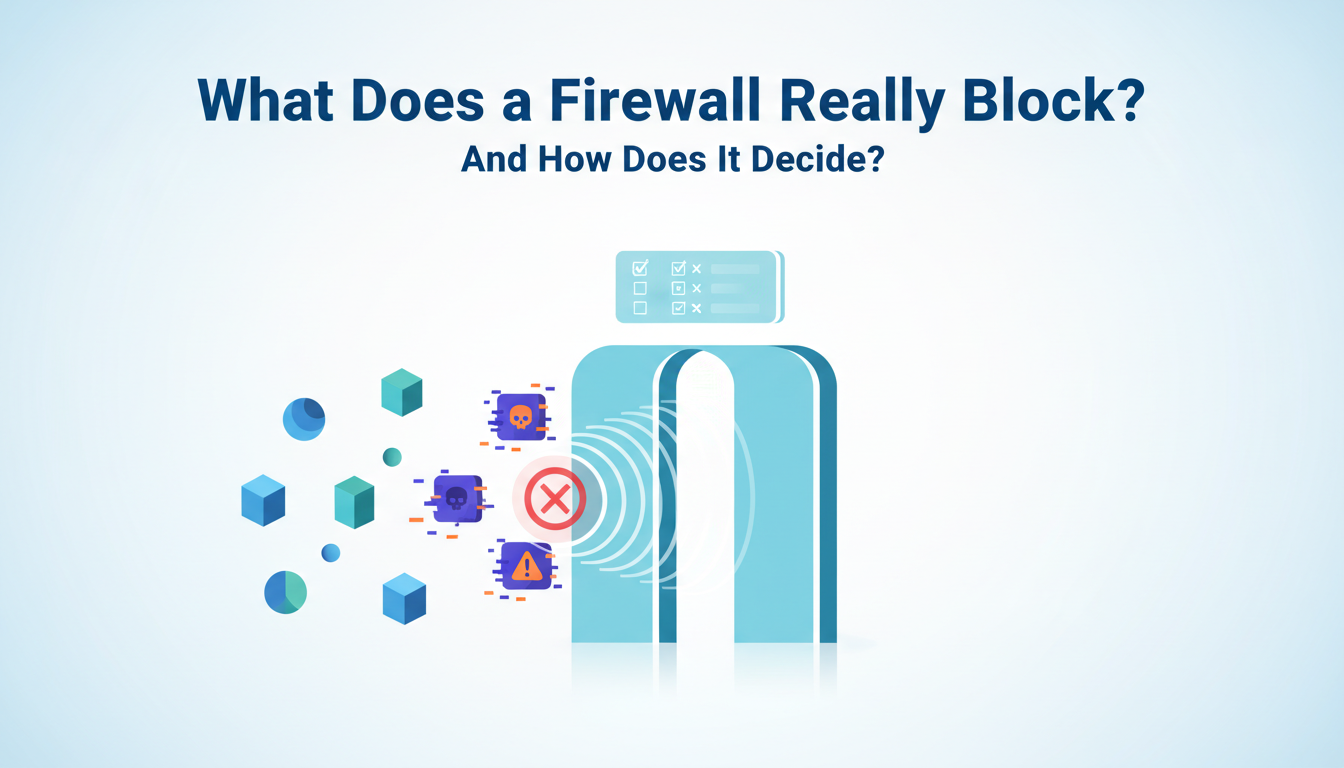
Ask most business owners what a firewall does and you’ll get some version of “it protects us from hackers.” And that’s not wrong — but it’s a bit like saying...
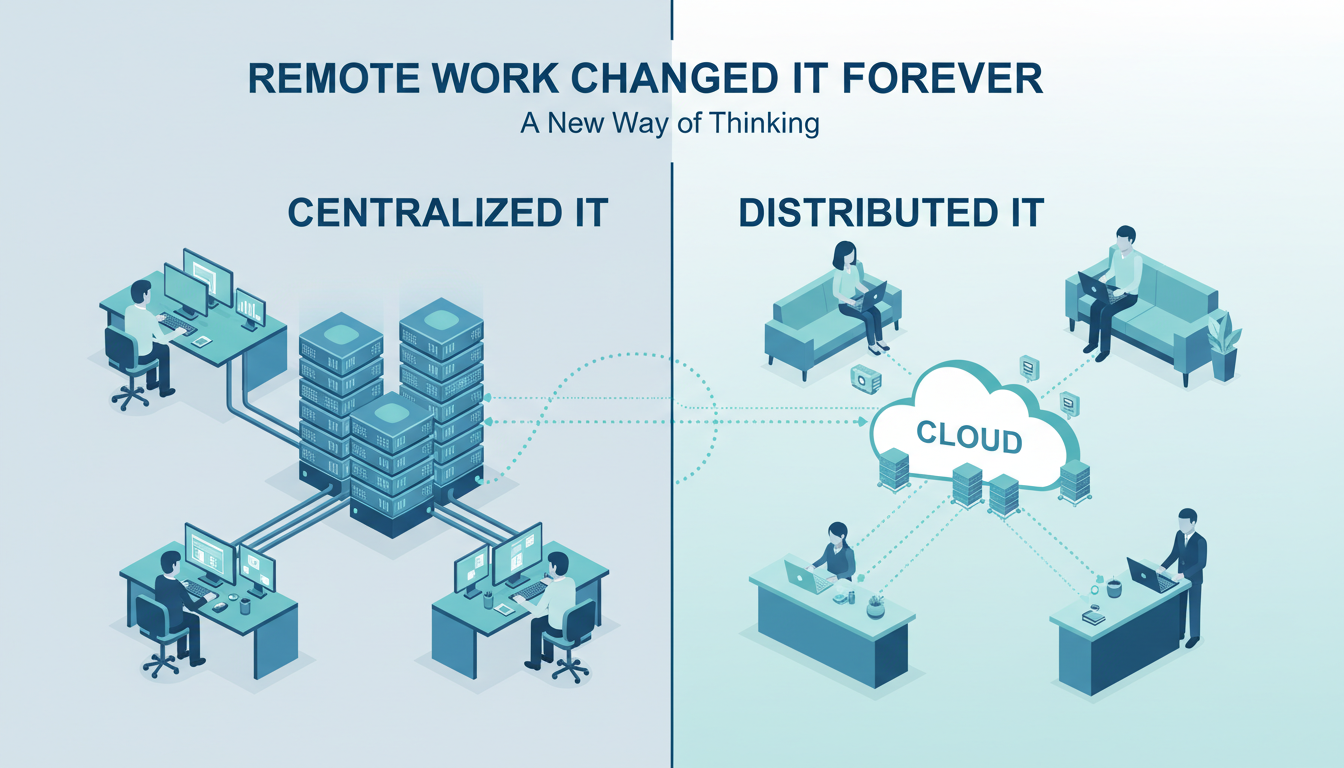
Let’s be honest: no one expected a global pandemic to be the cause of one of the biggest IT changes in modern business history. But here we are. What began...
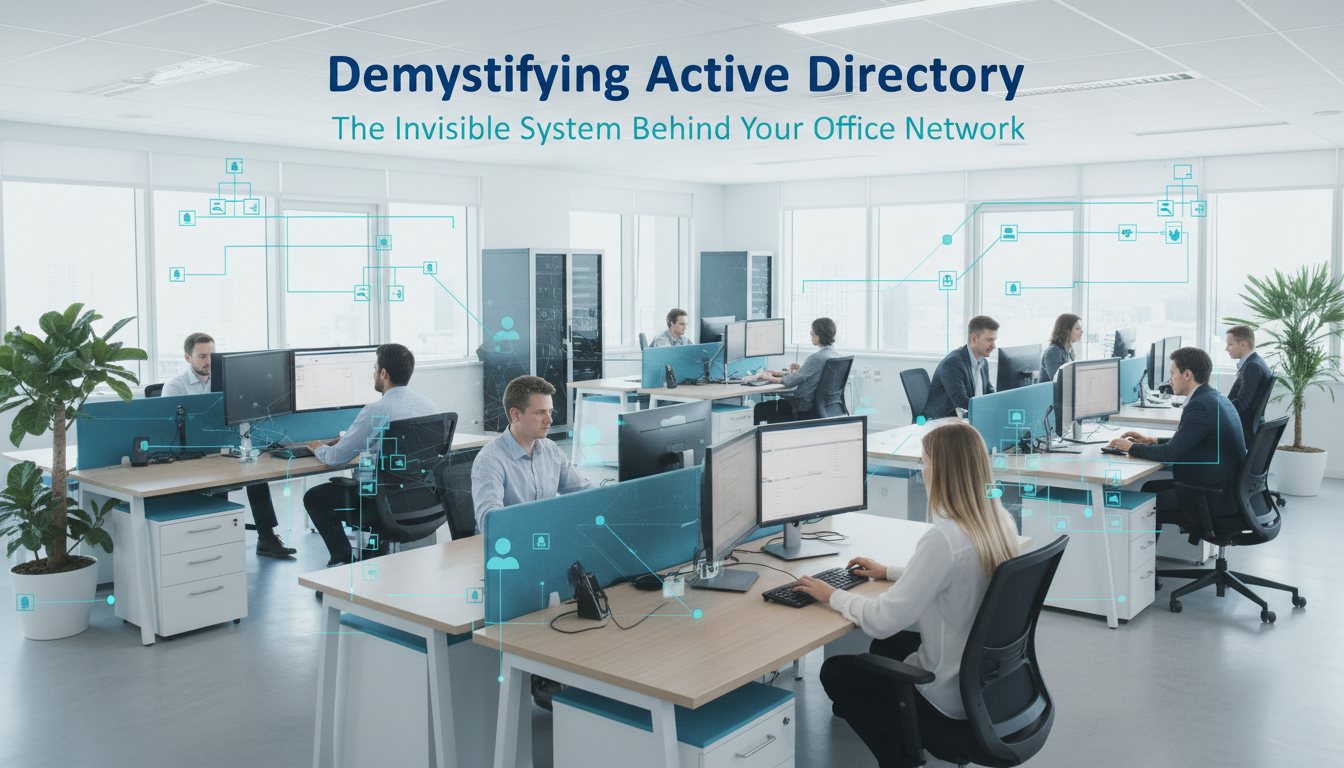
The Invisible System Running Most Office Networks Ever walked into a new office job, logged into your laptop with one username and password, and then seamlessly accessed the printer, shared...
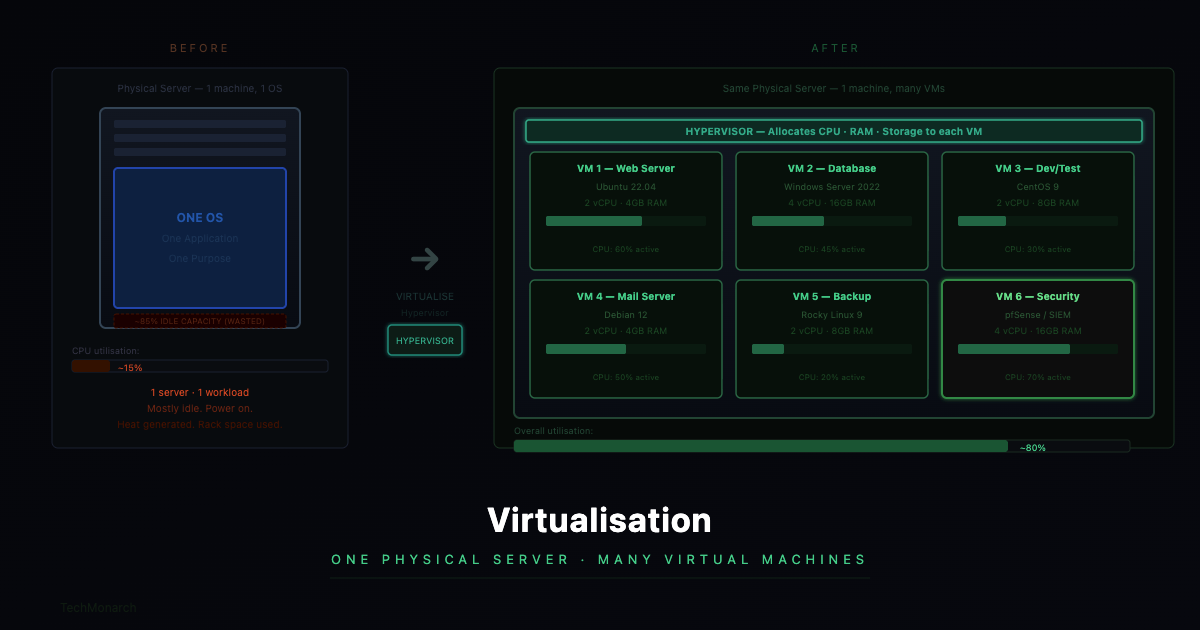
The Concept That Quietly Revolutionised Business IT 92% of businesses now use server virtualisation (Spiceworks 2025 survey) 5–15% → 70%+ Typical server utilisation jump after virtualisation — same hardware, dramatically...
From ‘My Laptop Isn’t Working’ to Fixed “My laptop isn’t connecting to the internet.” Four words. For the person saying them — usually ten minutes before a client call —...
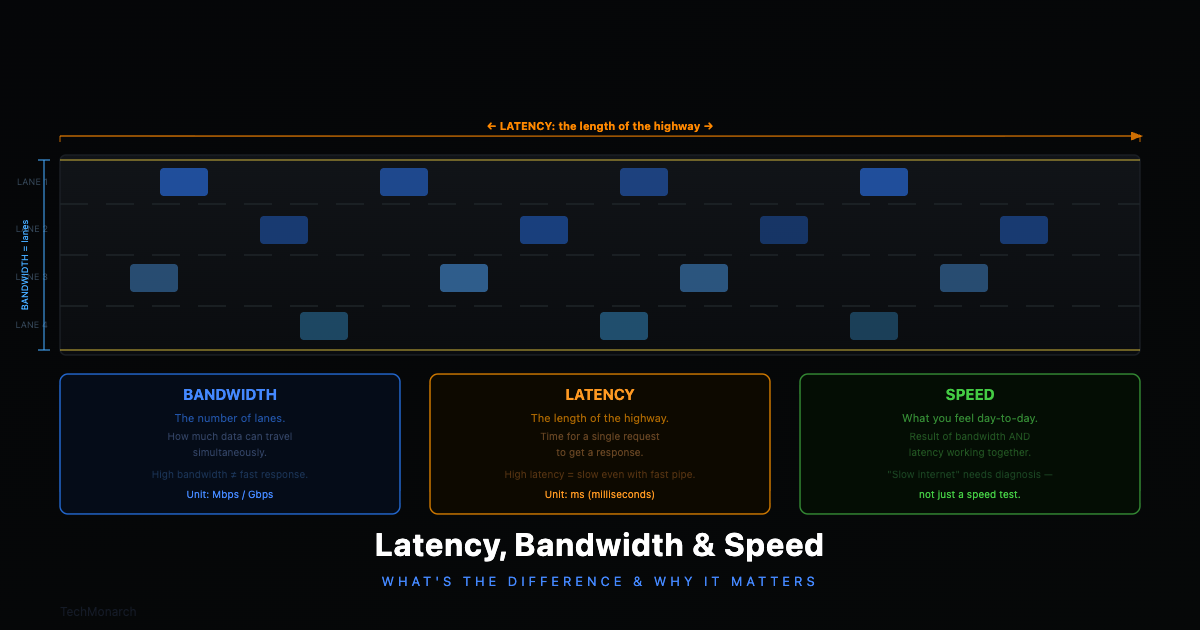
What’s the Actual Difference — and Why Does It Matter for Your Business? 100ms+ latency threshold where cloud app slowdowns become noticeably felt by users 200ms+ latency level where real-time...
Follow us to Stay updated with the latest IT trends and insights.
From cutting-edge trends to practical tips, our articles offer a wealth of knowledge
for IT enthusiasts at all levels.