Beyond Firewalls: Strengthening Your Business’s Cyber Defenses
As cybersecurity threats rapidly evolve, firewalls alone cannot ensure your…
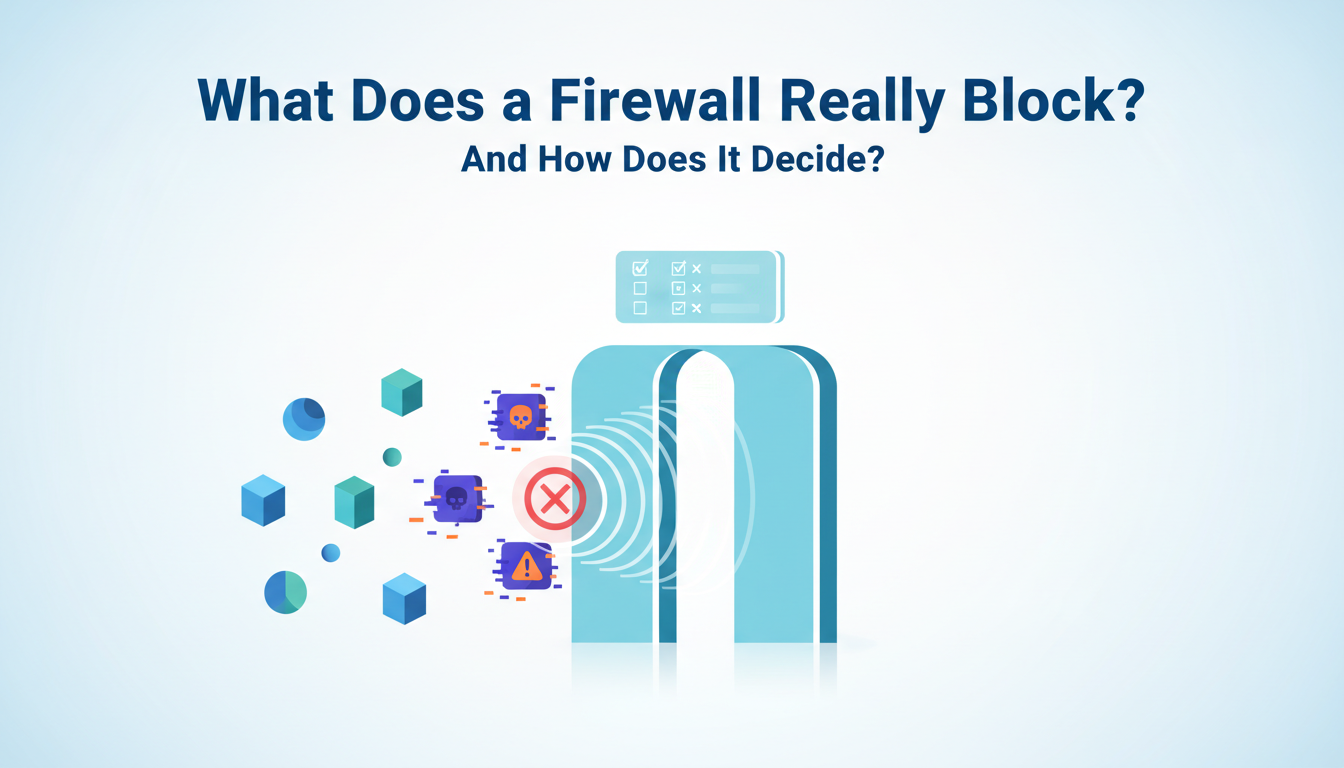
Ask most business owners what a firewall does and you’ll get some version of “it protects us from hackers.” And that’s not wrong — but it’s a bit like saying...
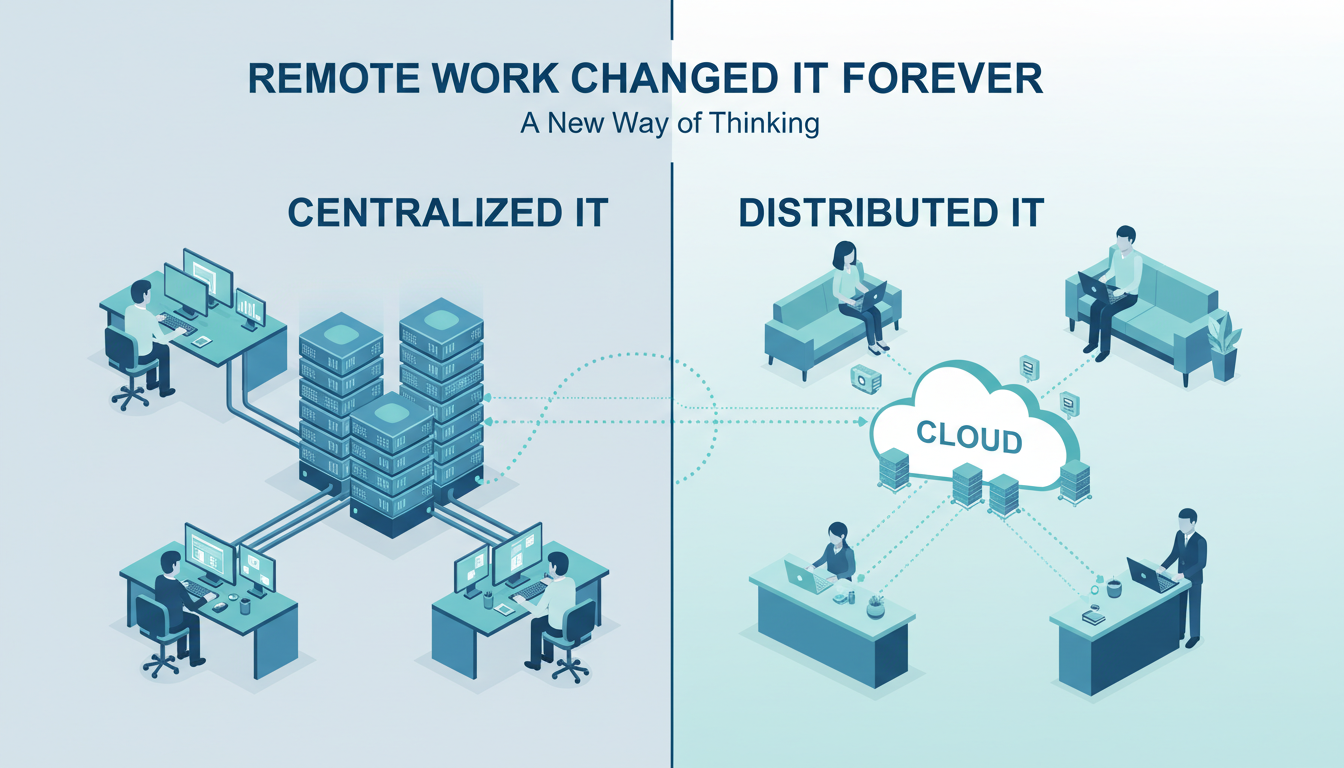
Let’s be honest: no one expected a global pandemic to be the cause of one of the biggest IT changes in modern business history. But here we are. What began...
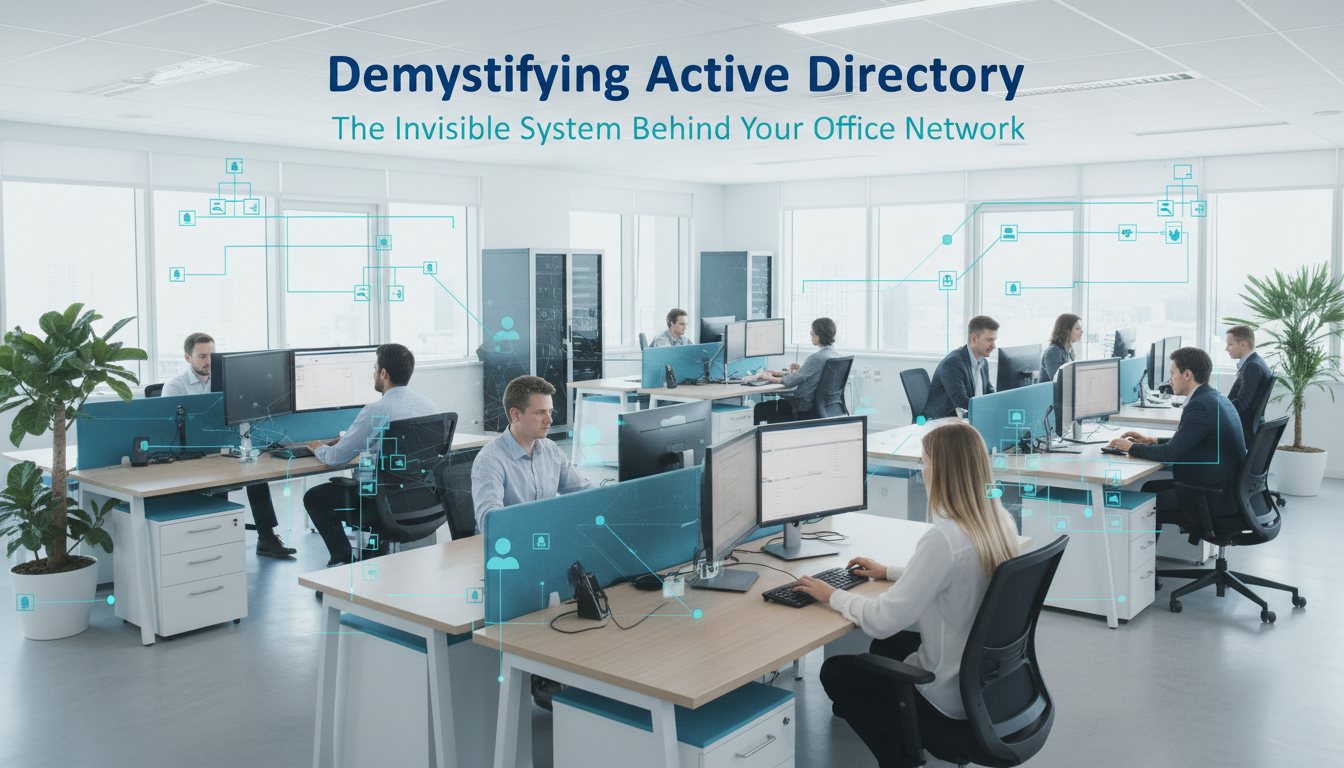
The Invisible System Running Most Office Networks Ever walked into a new office job, logged into your laptop with one username and password, and then seamlessly accessed the printer, shared...
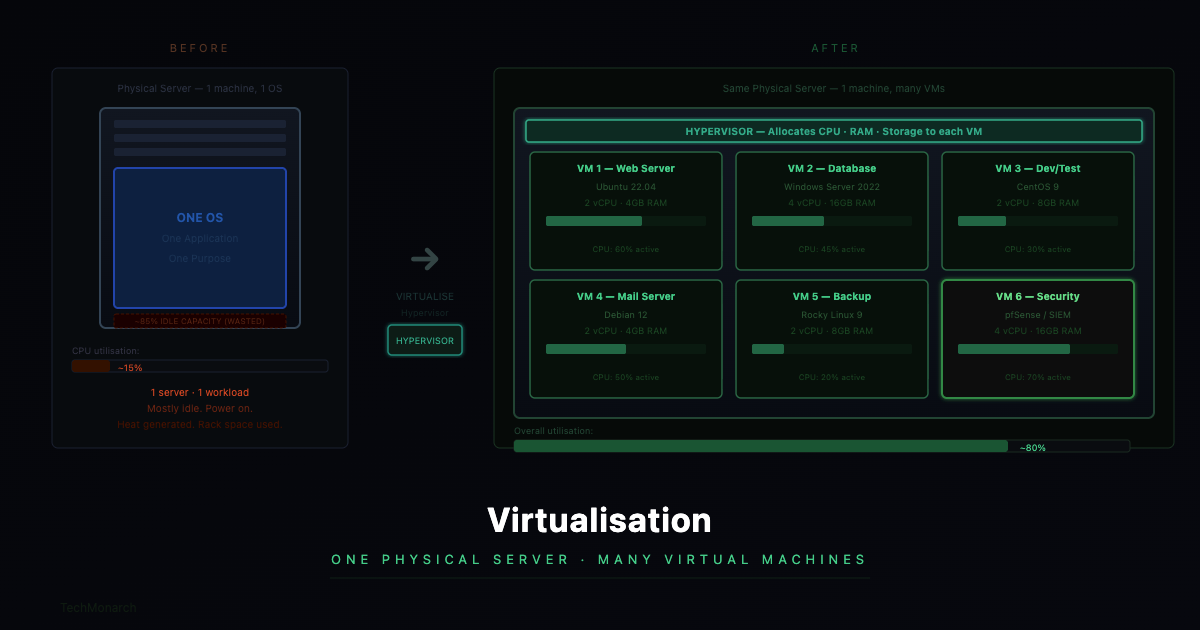
The Concept That Quietly Revolutionised Business IT 92% of businesses now use server virtualisation (Spiceworks 2025 survey) 5–15% → 70%+ Typical server utilisation jump after virtualisation — same hardware, dramatically...
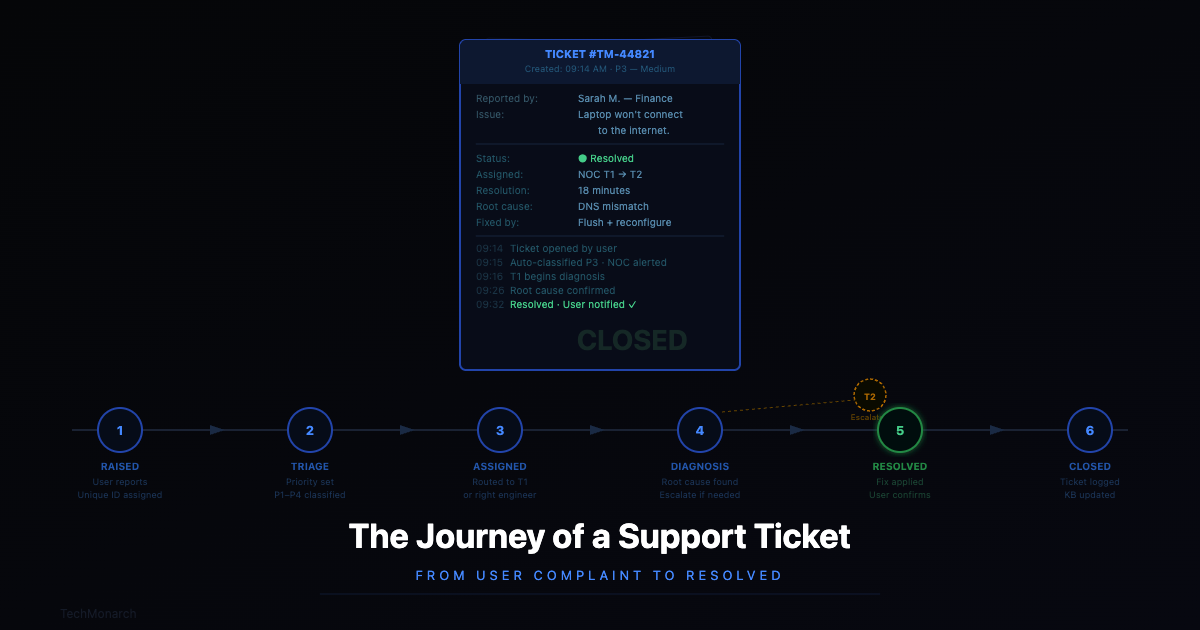
From ‘My Laptop Isn’t Working’ to Fixed “My laptop isn’t connecting to the internet.” Four words. For the person saying them — usually ten minutes before a client call —...
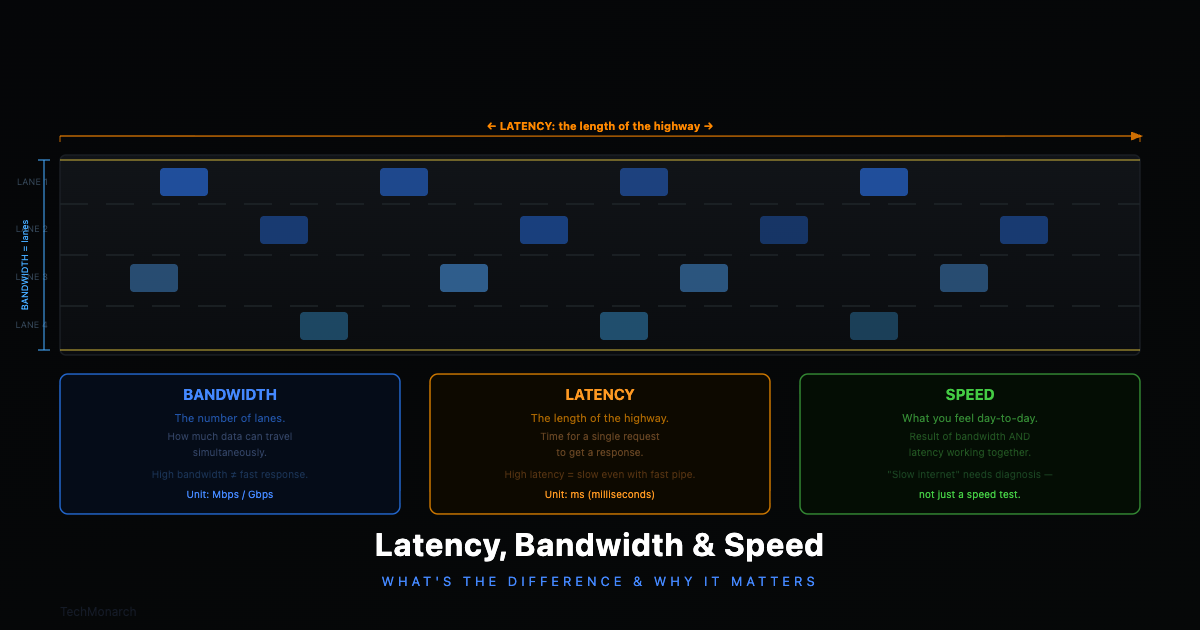
What’s the Actual Difference — and Why Does It Matter for Your Business? 100ms+ latency threshold where cloud app slowdowns become noticeably felt by users 200ms+ latency level where real-time...
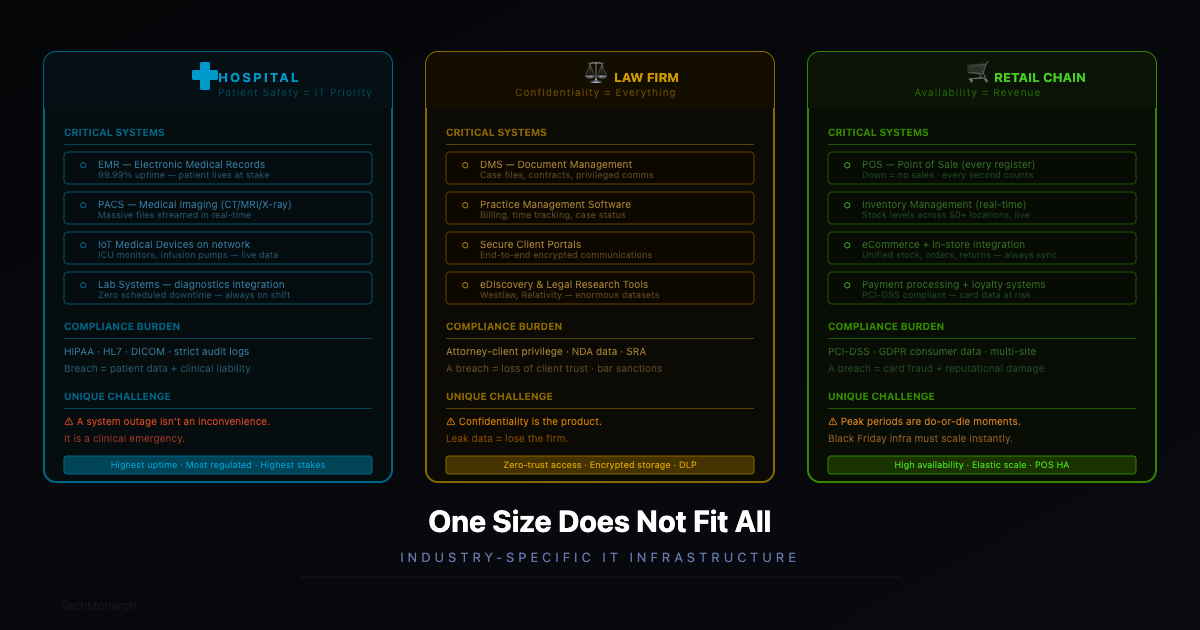
Someone once asked us why we don’t just offer a standard IT package — same setup for everyone, simpler to deliver, easier to price. It’s a fair question on the...
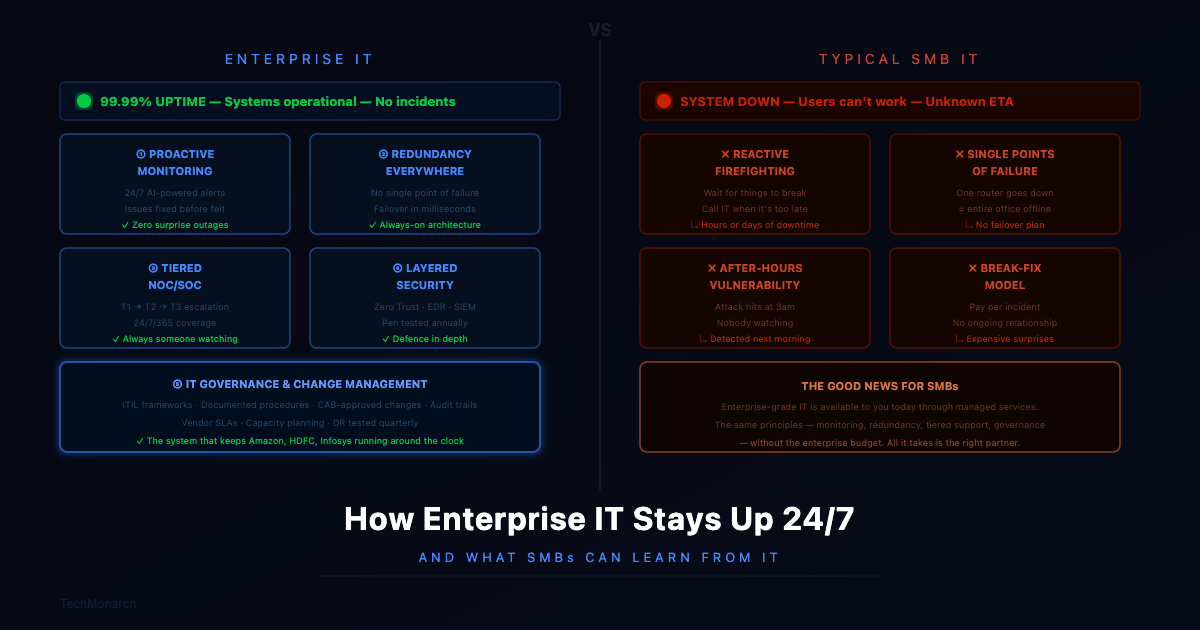
What SMBs Can Learn From It $300K+ estimated cost of one hour of downtime for SMBs (ITIC 2024) 60% of SMBs that suffer a cyberattack shut down within six months...
What Actually Happens 29 min Average eCrime breakout time in 2025 — down from 48 min in 2024 (CrowdStrike 2026 GTR) 27 sec Fastest observed attacker breakout time recorded —...
What They Actually Are and How to Pick the Right One If you’ve sat in a vendor demo recently, you’ve probably heard ‘cloud’ used about forty times while somehow leaving...
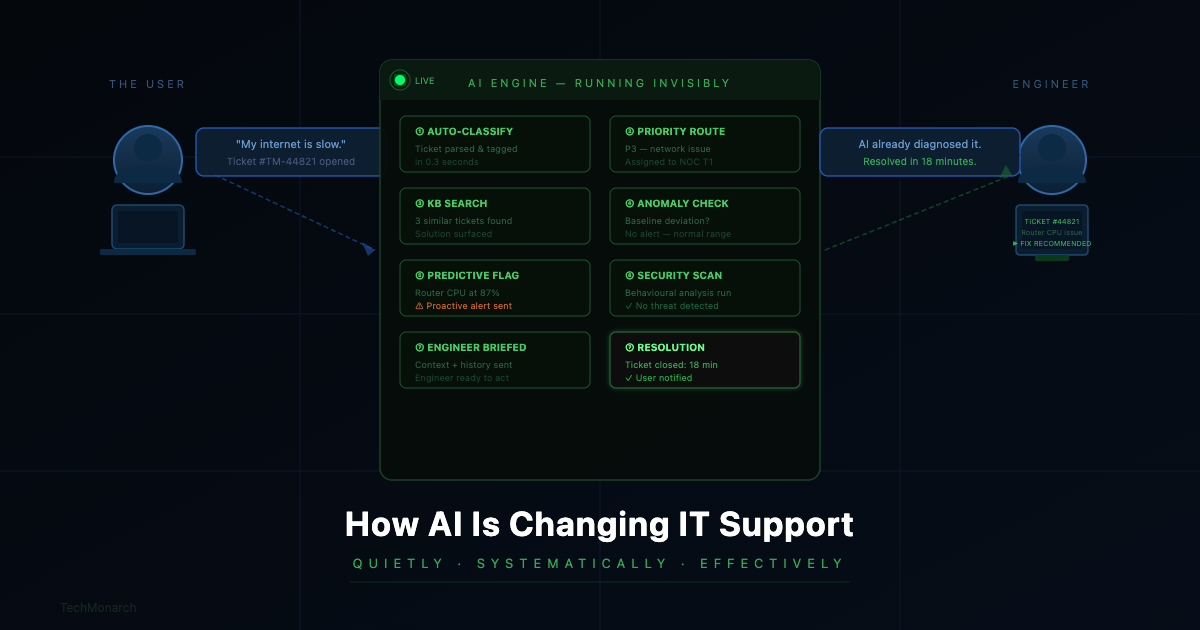
39% faster resolution times with AI helpdesk automation (ZenAdmin) 80% of routine inquiries handled without human intervention (Fullview) $3.50 returned for every $1 invested in AI customer service (McKinsey) 50%+...
How to Eliminate Repetitive IT Issues With Better Documentation Practices In the fast-paced world of IT, recurring technical problems can slowly carry away productivity and resources while making teams miserable. Herein...
Follow us to Stay updated with the latest IT trends and insights.
From cutting-edge trends to practical tips, our articles offer a wealth of knowledge
for IT enthusiasts at all levels.