Someone once asked us why we don’t just offer a standard IT package — same setup for everyone, simpler to deliver, easier to price. It’s a fair question on the surface. But spend one afternoon in a hospital ward, a law firm’s document room, and a retail store’s back office, and the answer becomes obvious.
The IT infrastructure running behind each of those environments is doing completely different things, protecting completely different kinds of information, and failing in completely different ways when something goes wrong. A configuration that works perfectly for a retailer would be a compliance disaster at a hospital. The security approach you’d use at a law firm would be overkill for a café and dangerously light for a healthcare clinic.
Let’s walk through all three. What their IT environments actually look like, what specifically has to work — and what happens when it doesn’t.
The Hospital
Healthcare IT operates under a constraint no other industry quite matches: when the system goes down, patient care is directly affected. That’s not an exaggeration. Clinical staff rely on IT for medication records, test results, patient histories, imaging, and real-time monitoring. An outage isn’t an inconvenience. It has clinical consequences.
Healthcare was the most targeted sector for cyberattacks in 2024 — 444 reported incidents in the US alone, more than any other critical infrastructure category. The average data breach cost healthcare organisations $9.8 million per incident. Ransomware attacks cause an average of 19 days of downtime, and 36% of affected facilities report increased medical complications as a direct result. These aren’t abstract risks.
The IT environment itself is genuinely complex. Doctors need fast access to EMR systems. Radiology runs PACS — picture archiving and communication systems — that push hundreds of megabytes of imaging data across the network constantly. Labs need their diagnostic equipment talking directly to patient record systems. ICU and OT environments may have medical devices connected to the network. And over all of this runs the administrative layer: billing, HR, pharmacy, appointments — all simultaneously, on a network that can’t have a maintenance window at 2am because someone’s always on shift.
What this demands, practically:
- Zero-downtime architecture — redundant servers, redundant links, automatic failover. There’s no time to switch systems by hand during an emergency.
- Network segmentation — clinical systems, medical devices, and administrative computers on separate segments. A ransomware attack that takes down billing should not be able to reach the EMR.
- High-bandwidth infrastructure — a single MRI scan can be 500MB. Radiology generates thousands. The network has to handle that volume without degrading.
- Airtight access control — patient records accessed only by those who need them, with audit logs of every access. Required by law, and critical for containing any breach.
WannaCry in 2017 took down significant parts of the UK’s NHS. Surgeries cancelled, ambulances diverted, patient records inaccessible. That wasn’t a hypothetical. It happened because the IT environments in those hospitals weren’t built for the environment they were operating in.
| TechMonarch & Healthcare IT in Ahmedabad We know healthcare IT has unique demands — the always-on infrastructure, compliance requirements, medical device integration, and the absolute priority of data security. Whether it’s a new clinic setup, hospital network expansion, or modernising ageing infrastructure, we build resilient healthcare IT environments built for clinical workflows. Serving healthcare businesses in Ahmedabad. Get in touch: www.techmonarch.com |
The Law Firm
The most important word in a law firm’s relationship with IT is confidentiality. Lawyers are professionally and legally obligated to protect client information. A data breach isn’t just a reputational and financial problem — it can put clients directly at risk, trigger regulatory action, and in serious cases, end a firm’s ability to practice.
And yet law firms are consistently among the more cyber-vulnerable organisations out there. They hold extraordinarily valuable data — M&A intelligence, litigation strategy, client financials, trade secrets — but are often seen (correctly) as less mature in IT security than the large corporations whose most sensitive matters they handle. 2024 saw a record 45 ransomware attacks on law firms, compromising 1.5 million records. The average breach cost $5.08 million, a 10% increase year on year. Nearly 40% of clients say they would leave a firm that suffered a breach.
At its core, a law firm’s IT environment is a document management ecosystem. Lawyers create, receive, review, annotate, version, store, and retrieve documents — thousands of them across dozens of active matters at any given time. A Document Management System (DMS) sits at the centre, handling organisation, version control, access permissions, and integration with billing and email.
Beyond the DMS: matter management software, legal research platforms, court filing systems, collaboration tools for clients and co-counsel. And because lawyers regularly work from courts, client offices, and home, remote access is a constant — which means it’s also a constant security consideration.
What this demands, practically:
- End-to-end encryption — client communications, file transfers, video calls. Many corporate clients now contractually require their legal advisors to meet specific security standards before engagement.
- Granular access control — not every lawyer in a firm needs access to every matter. Access should be restricted by client file, with audit trails. This is a legal obligation, not just best practice.
- Email security and archiving — phishing is the top entry point for law firm attacks. Immutable email archives are a compliance obligation and a commercial defence when firms are asked to produce correspondence in litigation.
- Tested business continuity — a system failure during a filing deadline isn’t just an IT problem. Missed court deadlines can carry serious legal penalties. Backups need to be tested, not just scheduled.
- Secure remote access — VPN with MFA and device management policies. Remote access without these controls is often the weakest link in an otherwise sound environment.
The data law firms hold makes them high-value targets. Their historically light IT investment makes them accessible ones. That combination is exactly why attacks on legal firms are rising.
| TechMonarch & Legal IT in Ahmedabad We’ve worked with professional services firms that need the right combination of document security, reliable performance, and seamless remote access. From secure DMS environments to email security and VPN infrastructure, we build IT environments that meet the confidentiality standards the legal profession requires. Serving law firms in Ahmedabad. |
The Retail Chain
Retail IT doesn’t get the same attention as healthcare or legal, but its failure modes are visible in a way most industries never experience — they play out directly in front of customers, in real time.
Every completed transaction triggers a chain of IT events: the sale is processed, inventory is updated, loyalty points are recorded, payment data is transmitted, financial records are adjusted. When that chain breaks, the business doesn’t just slow down. It stops, publicly, while customers are watching.
POS outages cost the average retailer around $4,700 per minute in lost sales. Retail e-commerce platforms lose between $1 million and $2 million per hour during peak seasons. 36% of e-commerce businesses reported a site outage in the past year. And 40% of customers who experience a technical failure will go to a competitor and stay there.
For a retail chain operating across multiple locations — say, several outlets across Ahmedabad with a central warehouse and an e-commerce presence — the IT complexity compounds quickly. Each location needs reliable connectivity, a working POS, and real-time sync with central inventory. Head office needs visibility across all sites. The warehouse has its own systems. The e-commerce platform needs to reflect accurate stock at all times. And during peak periods — Diwali, end-of-season sales — the entire stack needs to handle multiples of its normal load.
What this demands, practically:
- POS with offline resilience — the ability to process transactions locally even if internet connectivity drops, syncing when it’s restored. Hardware that’s robust and quickly replaceable.
- Multi-site network management — five locations means five networks to monitor and secure. Centralised management lets the IT team push configuration changes and respond to issues at any location from a single dashboard.
- Real-time inventory sync — between stores, warehouse, and e-commerce. Nothing erodes customer trust faster than buying online and being told it’s out of stock, or driving to a store for something the website said was available.
- PCI-DSS compliance — every organisation processing card payments must comply. Payment systems need isolated, secure network segments and regular assessments. Non-compliance carries severe penalties.
- Scalable infrastructure for peak periods — systems that can handle Diwali traffic, not just average Tuesday traffic. Cloud infrastructure that flexes with demand. Load testing before major trading periods, not after.
A retail chain’s e-commerce platform going down during a sale event can cost lakhs in lost revenue per hour. A POS failure across multiple stores on a busy weekend shuts the operation down in front of its customers. Retail IT failure is the least forgiving kind.
| TechMonarch & Retail IT in Ahmedabad Retail IT is as much about reliability at the customer touchpoint as it is about back-office efficiency. We help retail businesses in Ahmedabad design and manage infrastructure that keeps POS systems running, networks connected across locations, and inventory systems synchronised. Get in touch: www.techmonarch.com |
Side by Side
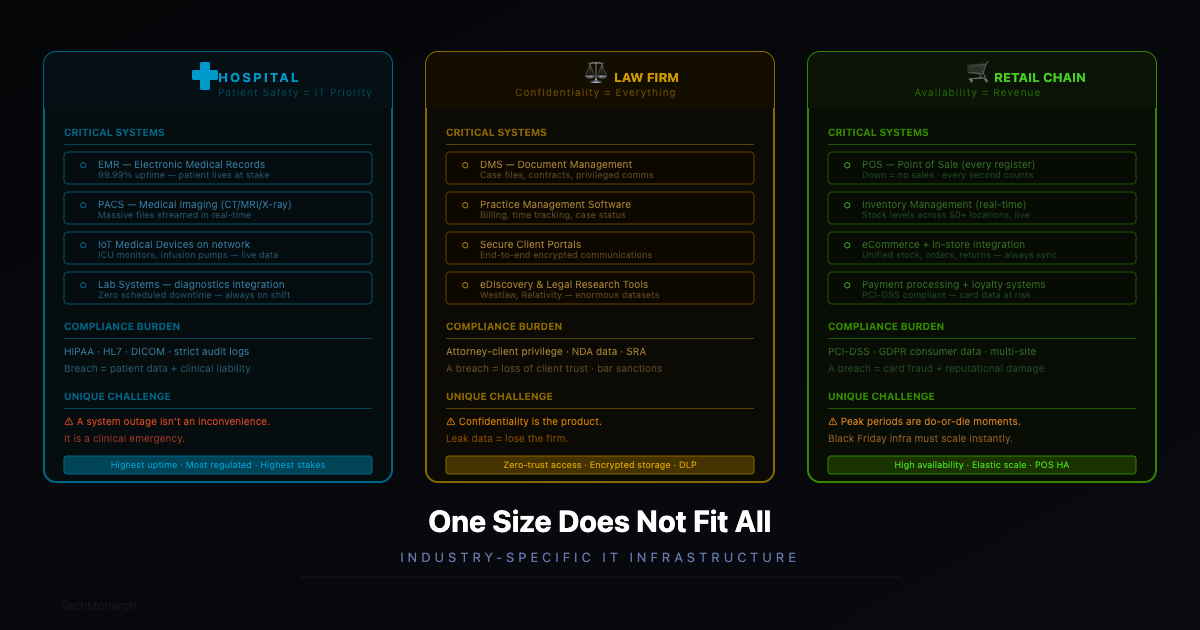
The key differences at a glance:
| Hospital | Law Firm | Retail Chain |
| Top priority | Zero downtime & patient data security | Confidentiality & document security | POS reliability & inventory sync |
| Biggest IT risk | System outage affecting patient care | Data breach or compliance failure | Downtime at peak trading hours |
| Critical systems | EMR, PACS, lab systems, medical devices | DMS, billing, email, remote access | POS, ERP, inventory, e-commerce |
| Compliance | DISHA, local health regulations | Bar council rules, client privilege | PCI-DSS, GST systems |
| Connectivity need | Highly redundant, always-on | Secure, encrypted, VPN-heavy | Multi-site, real-time sync |
Table: Key IT differences across healthcare, legal, and retail environments

What All Three Have in Common
For all their differences, a hospital, a law firm, and a retail chain need three things from their IT: reliability, security, and a partner who understands the context.
Reliability looks different in each case — patient safety, missed legal deadlines, or customers walking out — but the requirement is the same. The infrastructure has to work, consistently, when it’s needed most. Security covers different data types and different compliance frameworks, but every one of these organisations holds something that has real consequences if it’s compromised.
The context piece is the one that’s easiest to skip and hardest to fake. Generic IT support — good at fixing computers but unfamiliar with EMR systems, legal DMS platforms, or retail ERP integrations — will always fall short in these environments. The difference between IT that works and IT that actually fits is whether the people setting it up understand not just the technology, but the business it’s running inside.
| Industry-Aware IT Support — That’s What TechMonarch Brings Every business is different. The IT setup that works for a manufacturing company in Ahmedabad may be entirely wrong for a healthcare clinic or a retail chain. We take time to understand your industry, your workflows, your compliance requirements, and your growth plans — before we recommend anything. |
The Short Version
If an IT provider offers you a solution without first asking in detail about your industry, your operations, your users, and your compliance obligations — that’s worth noting. Good IT isn’t just technically correct. It fits the environment it’s built for.
Whether you run a hospital, a law firm, a retail chain, or anything in between — the right place to start is: tell me about your business. Everything follows from there.
Recent Comments
- No comments to show
